San Francisco – The task of teachers to teach Original titles – and maybe vaguely good and Attractive – For booksInformationOn that day Coding method And on Programming It is not simple. Sometimes we limit ourselves to being tactful, to go without, but without courage, to fall into banality, and at other times we limit ourselves to similes, similes, or Definitely ugly titlesIt also represents an original way of organizing and describing topics.
During a visit to California in recent weeks, A The VMware Explore conference was organized in personWe took the opportunity to look at the most popular and most loved titles from Programmers and experts the cloud Americans (and not only), we get it A round of books Between good and funny, sometimes bordering on the almost grotesque. Think about it, in highlights for programmers, a Fluent python It has Peyton distilled. Some of them have InternetAnd All are affordable – Obviously in English – from Italy too, sometimes with a small extra charge.
The IT Architect Series: Stories from the Field, Volume 1John Yanni Arrasjit and Matthew Wood (2020)
Not science fiction, but Real life stories: What is it like to personally participate in a large IT project when everything turns out to be a disaster? A horror story? 35 leading IT professionals recount their adventures in the world’s most challenging data centers, revealing why they happened. Failures And Accidents More or less seriously, sharing lessons learned and revealing what they would have done – in retrospect – differently. In short, a read to avoid Learn the hard way From mistakes that are best never made.
Practical IoT Hacking: The Definitive Guide to Hacking the Internet of ThingsFotios Chantziz and Ioannis Stais (2021)
A practical guide to attack, written by security experts of the Internet of Things A conceptual guide to making the most of IoT systems and devices, starting with the best achievements of 5 researchers specializing in cybersecurity. From the most common contemporary threats to emerging modeling, not just security attack: Vlan hopping, Mqtt authentication cracking, UPnP abuses, mDns poisoning and Ws-Discovery attacks, also go through Rfid devices. From technology, everything you need to know Penetration (and to protect against hackers) one Smart homeFrom wireless alarms to security cameras, to Smart appliances.
The new normal in information technologyGregory Smith (2022)

“Gamer. Professional beer expert. Food specialist. Hardcore zombie geek. Web ninja. Troublemaker.”






More Stories
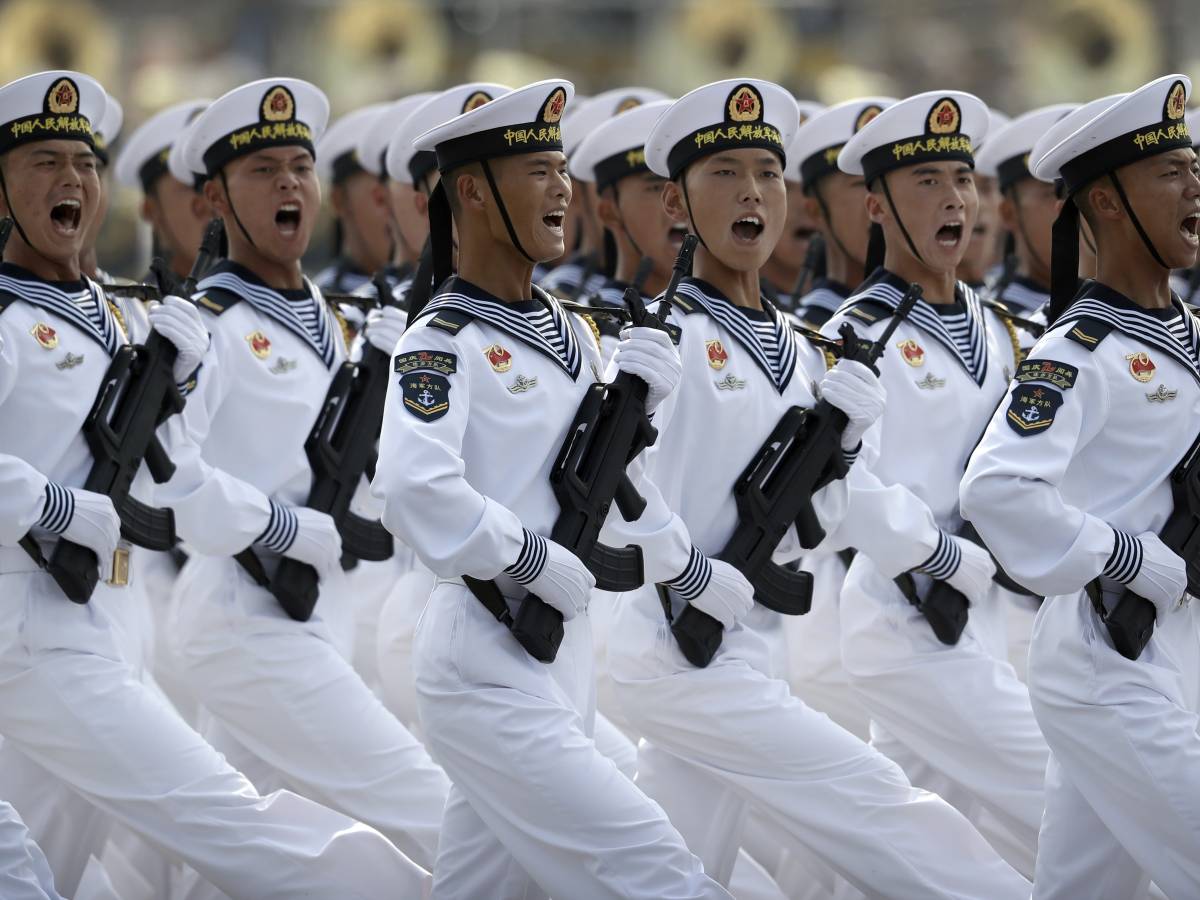
A Chinese outpost a stone's throw from the US: the latest secret revelation
Romano Prodi: Mine's not an attack on Schlein, but it's better not to have a name on the symbol
Snow, low elevation, will fall in affected areas from Tuesday onwards